World’s Largest Vaccine Maker to Develop New $16 Million AI-Optimized ‘Disease X’ Pandemic Bird Flu Jab Using Insect DNA
Serum Institute of India partners with CEPI and Houston Methodist to generate prototype vaccine targeting H5N1 avian influenza within 100 days’ time.

The Coalition for Epidemic Preparedness Innovations (CEPI) is collaborating with the world’s largest vaccine manufacturer, Serum Institute of India (SII), and Houston Methodist to develop a new pandemic vaccine with artificial intelligence (AI) that targets H5N1 avian influenza “bird flu,” according to a CEPI press release.
CEPI was launched at Davos in 2017 by the World Economic Forum (WEF), the Bill & Melinda Gates Foundation, and several world governments.
SII supplies vaccines to more than 170 countries and is “well known for its rapid response work during infectious disease outbreaks.”
The new project will be supported by up to $16.4 million.
The effort is meant to “boost pandemic response preparedness” for bird flu and serve “as a prototype for a potential Disease X—an as-yet-unknown pathogen with pandemic potential.”
The new avian flu jab will utilize a ‘baculovirus’ vaccine platform, a system that uses genetically modified baculoviruses (DNA viruses that infect insects, especially their larval stages) to produce recombinant proteins in insect cells.
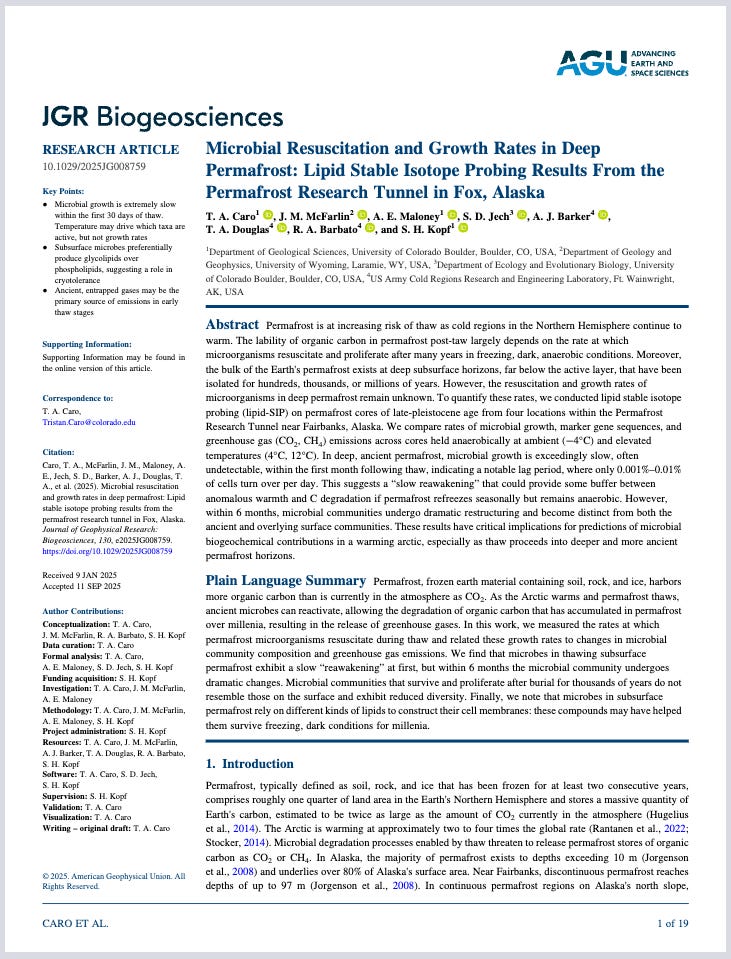
SII will “produce and compare two H5 antigens for a recombinant protein vaccine: a wild-type and an AI-optimised, broad-spectrum H5 antigen designed by scientists at Houston Methodist Research Institute.”
The vaccine is supposed to work “across multiple strains of H5 viruses, rather than just one.”
CEPI claims this makes the new injection “particularly suited for use in unpredictable outbreak situations.”
The idea is to accomplish “a fast response to a future pandemic threat.”
The work will also “serve as proof of concept for using AI to design vaccine antigens,” proteins said to trigger an immune response.
The new bird flu vaccine will be “designed to power up global readiness to tackle pandemic threats, from early-stage vaccine development through to global manufacture and supply,” said CEPI CEO Dr. Richard Hatchett.
“With a potential pandemic influenza vaccine candidate already in development on a validated platform, and with a vaccine manufacturing juggernaut ready to go, the world’s disease defences will be poised to respond swiftly with new vaccines, potentially in 100 days, should a flu virus erupt into a potentially deadly and fast-spreading human pandemic.”
The goal is for the jabs to be “quickly created.”
SII and CEPI see their new bird flu jab as an “ideal candidate for faster responses against potential pandemic diseases.”
“This aligns with CEPI’s 100 Days Mission—a goal embraced by leaders of the G7 and G20 to accelerate vaccine development to within 100 days of identifying a pandemic threat,” the press release reads.
SII CEO Adar Poonawalla said the new platform “gives us the ability to rapidly develop and produce vaccines for emerging threats. This project will test that readiness in real terms, reinforcing our commitment to pandemic preparedness. The learnings will not only support faster response times but also ensure that effective vaccines can reach vulnerable populations without delay.”
The project will also leverage the expertise of the U.K.’s Francis Crick Institute for testing, according to the press release:
“The project will also leverage the expertise of CEPI’s Preclinical Model Network and Centralized Laboratory Network members—the UK Health Security Agency and the Medicines and Healthcare products Regulatory Agency—alongside the Francis Crick Institute, to conduct key testing activities to demonstrate that the wild-type and AI-optimised H5 vaccines are fit for purpose.”
Trump Admin Ties to Francis Crick Institute
Back in February, this website reported that the CDC and FDA were “actively participating” in virtual meetings with the World Health Organization (WHO) at the Crick Worldwide Influenza Center in London, which is part of the Francis Crick Institute.
The top U.S. health agencies were participating with the WHO despite President Donald Trump signing an executive order on January 20, 2025 that was supposed to officially withdraw the United States from the WHO.
That order explicitly commanded to “recall and reassign United States Government personnel or contractors working in any capacity with the WHO.”
But the Trump administration made concessions for influenza bird flu efforts, signaling its role in orchestrating another pandemic.
President Trump has since announced the development of a “next-generation, universal vaccine platform” called ‘Generation Gold Standard’ that will focus on bird flu jab creation.
Gold Standard represents the institutionalization of a staggering conflict of interest.
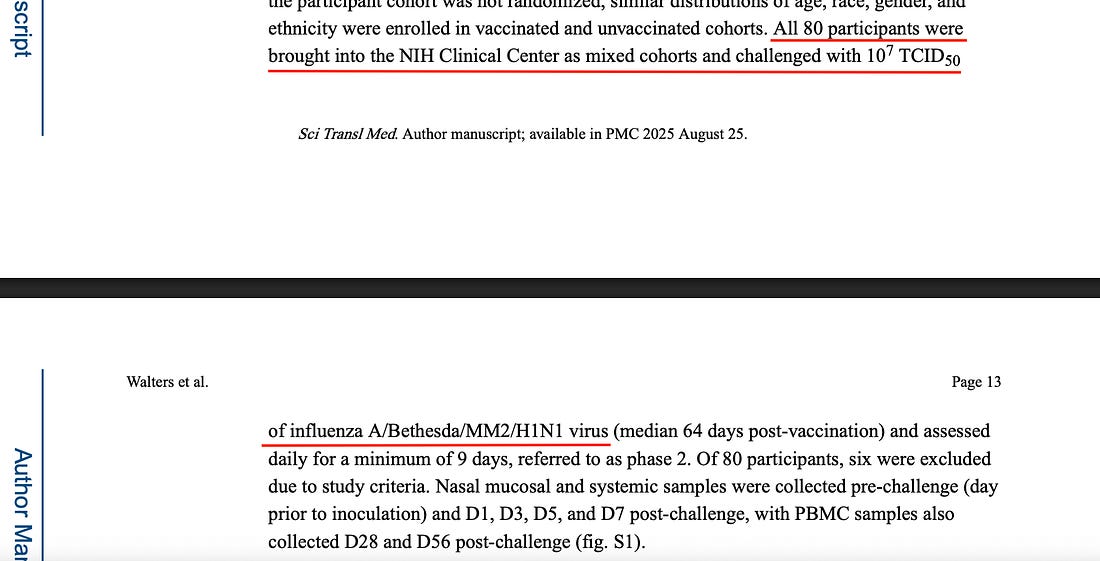
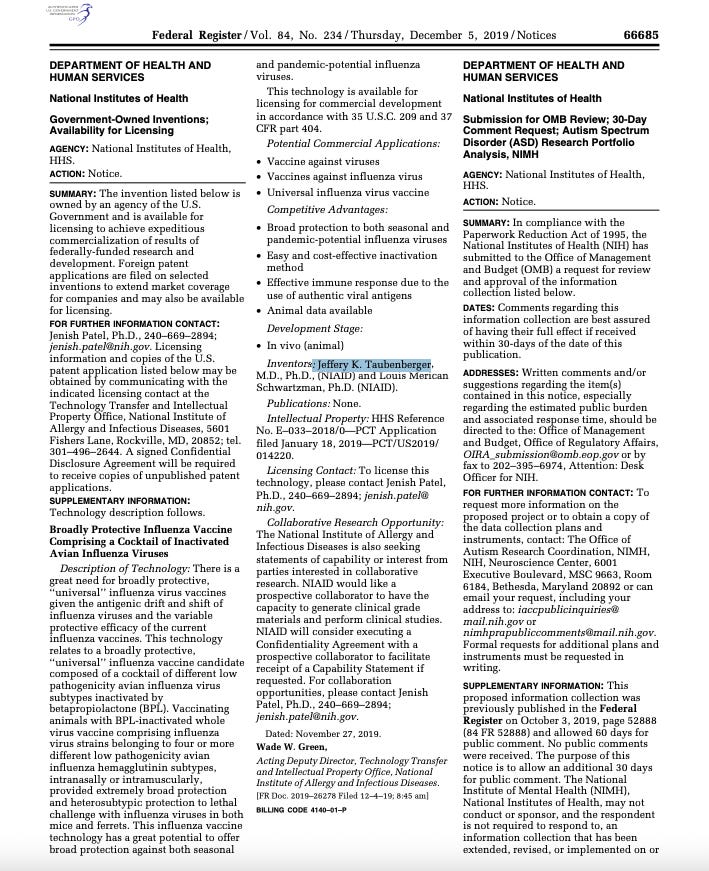
NIAID Director Dr. Jeffery Taubenberger—who now oversees U.S. taxpayer-funded gain-of-function experiments creating new bird-flu viruses—is also a named inventor on the federal patent for the program’s beta-propiolactone (BPL)-inactivated “universal” bird flu vaccine at the center of Gold Standard.
This is despite BPL being a known carcinogen classified as a ‘Group 1B’ substance in Europe and ‘Group 2B’ in the U.S.
In other words, the same official directing the creation of potentially pandemic-causing bird flu pathogens is positioned to personally profit from the vaccine meant to counter them, raising profound national-security, informed-consent, and conflict-of-interest concerns at the very heart of America’s pandemic-preparedness system.
Dr. Redfield’s 2022 Bird Flu Warning
Former CDC Director Dr. Robert Redfield has predicted that a bird flu pandemic will be much worse than COVID.
Dr. Redfield expects a bird flu pandemic to “have significant mortality, in the ten to fifteen percent range.”
“I don’t believe [COVID] is the ‘great pandemic,’” he said in a March 2022 interview. “I believe the great pandemic is still in the future. And that’s going to be a bird flu pandemic from man. It’s going to have significant mortality, in the ten to fifteen percent range. It’s going to be trouble. And we should get prepared for it.”
Redfield emphasized the danger of this coming bird flu pandemic.
“I do believe that the pandemic risk is of greater risk to the national security of the United States than Korea, China, Russia, [and] Iran. And we ought to start investing proportional to that national security risk so we’re prepared. Unfortunately, we’re not more prepared today than we were when the [COVID] pandemic hit when I was CDC director. And we need to make that proportional investment so that we are prepared.”
Taken together, the CEPI-Gates-WEF partnership, the Trump administration’s Gold Standard program, and NIAID’s ongoing gain-of-function work form a seamless triad of power—where global health bureaucrats, government scientists, and private vaccine empires converge under the banner of “preparedness,” using taxpayer money and AI-driven biotechnologies to design both the next outbreak and the product to follow it.












Recent Comments